...
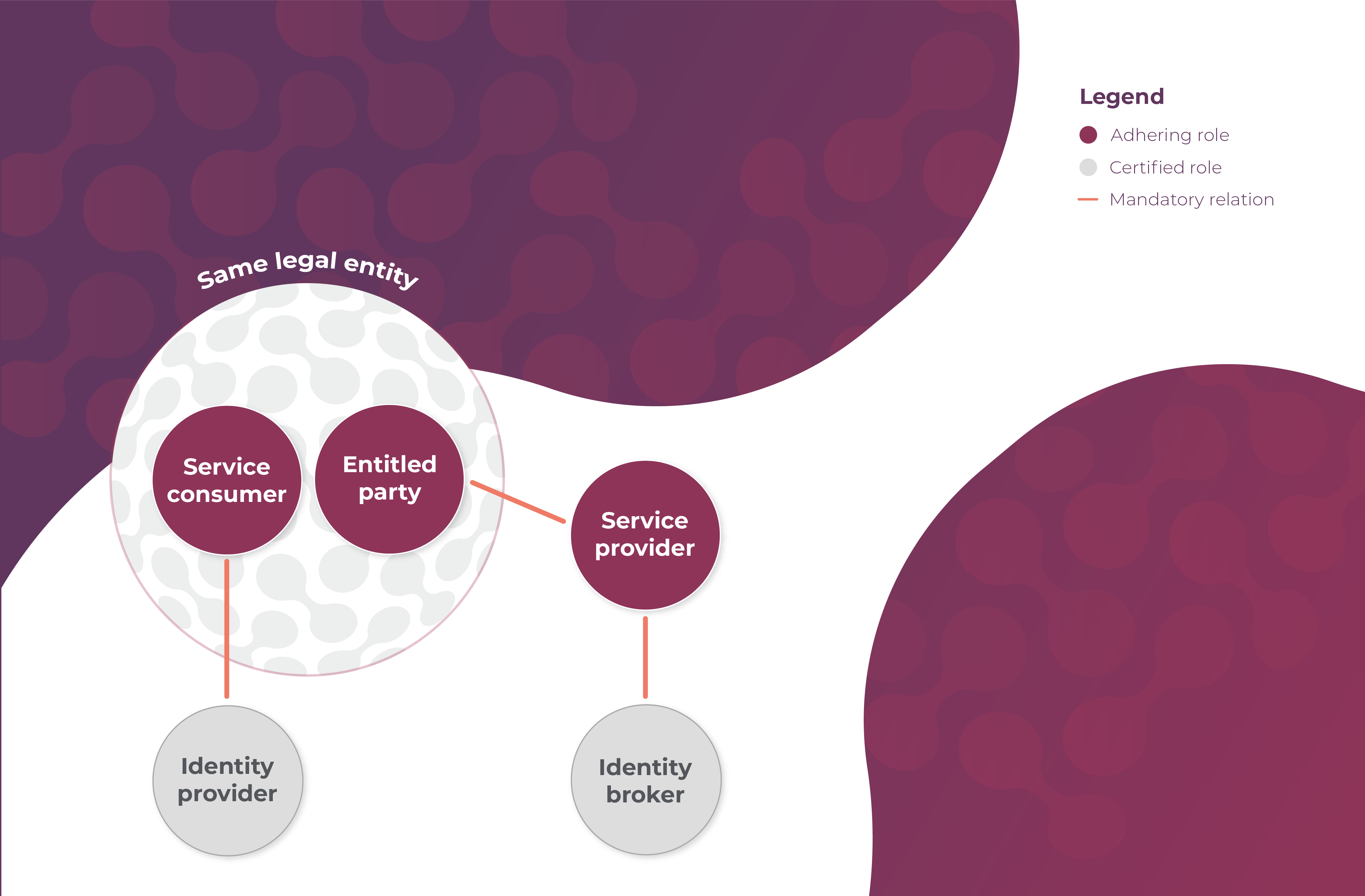
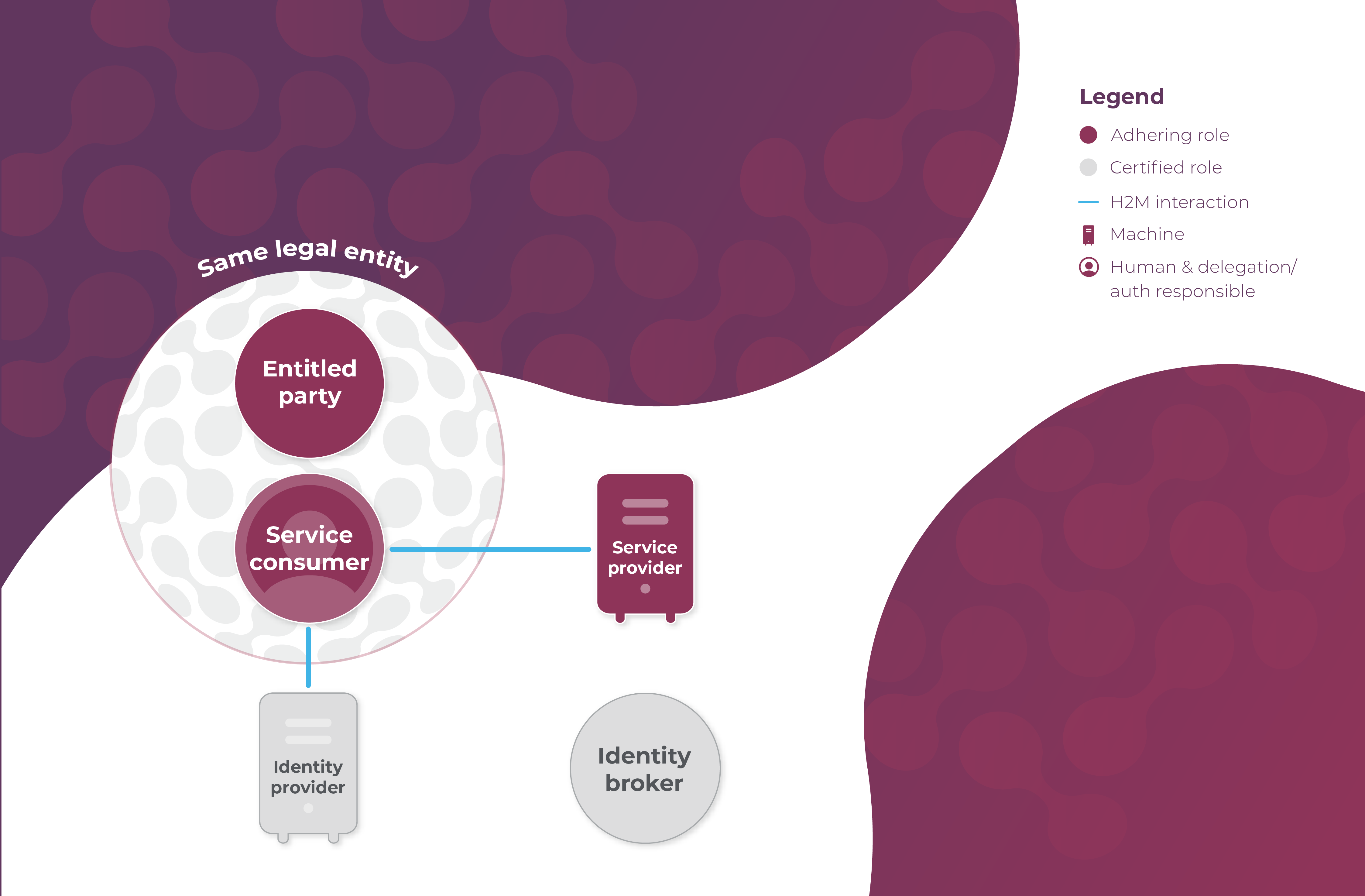
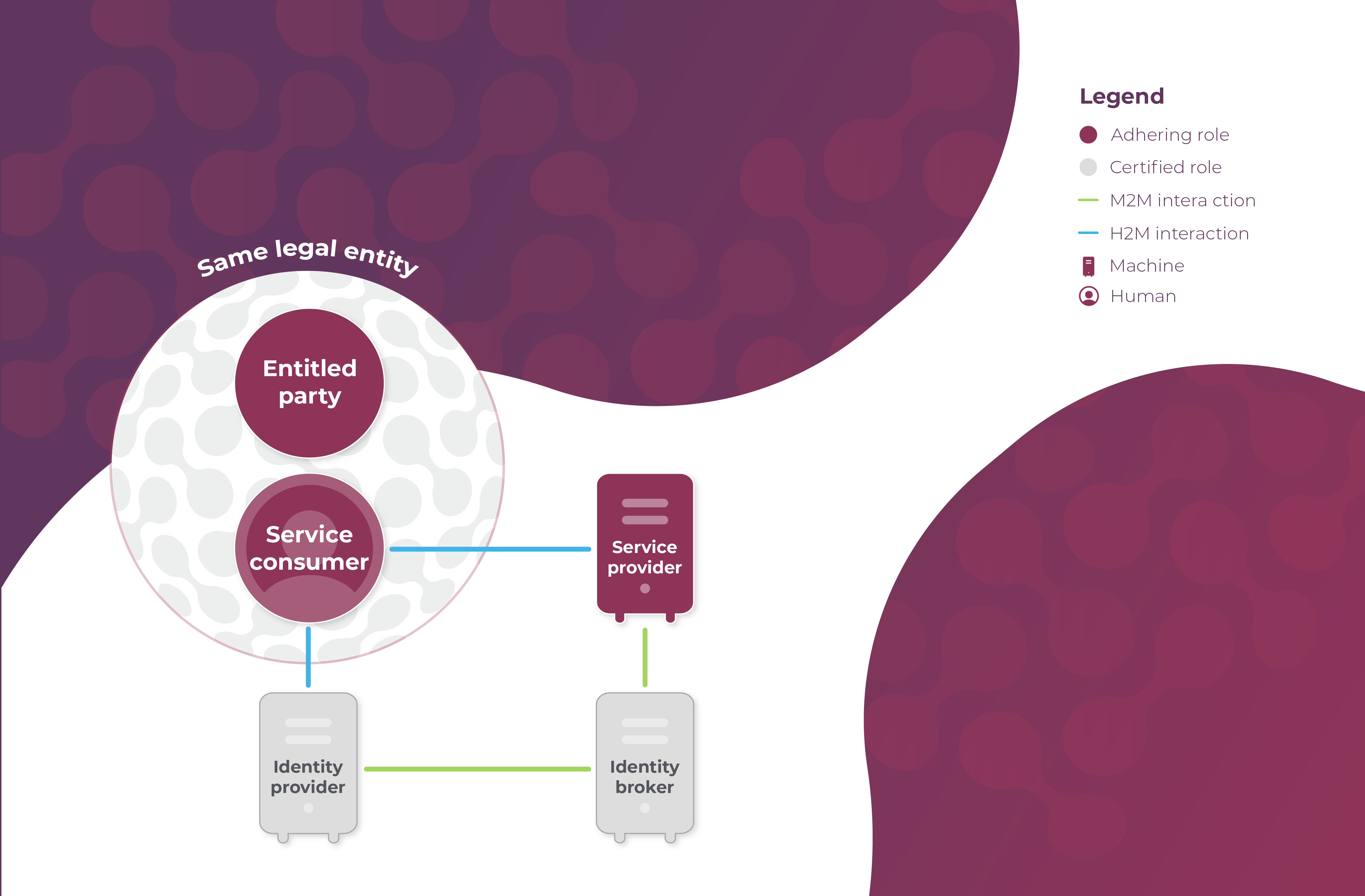
- As always, a mandatory relation between the Entitled Party (Party A) and the Service Provider (Party B) establishes the entitlements of the Entitled Party (Party A);
- A mandatory relation between the Service Provider and the Identity Broker covers the use of Identity Broker Z's services, including a connection to several Identity Providers, by the Service Provider (Party B);
- A mandatory relation between the Service Consumer (Party A) and Identity Provider Y covers the use of Identity Provider Y's keycards by the the Service Consumer's (Party A's) humans, including Human X.
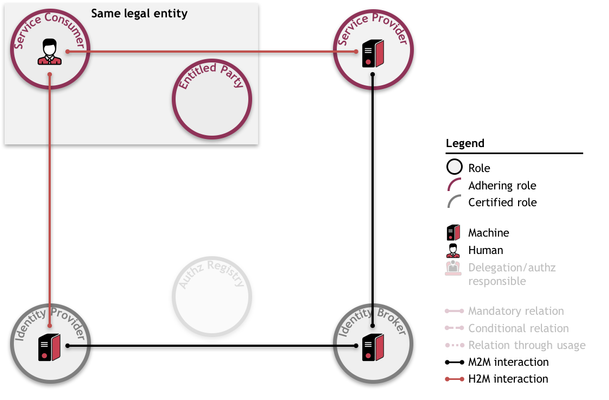
As depicted:
Prerequisites
...
The prerequisites in bold are depicted as follows:
Use case
The use case consists of the following steps:
- The Human Service Consumer (Human X) requests a service from the Service Provider (Party B);
- The Service Provider (Party B) requests a login from the Identity Broker (Z);
- The Identity Broker (Z) asks the Human Service Consumer (Human X) to select his Identity Provider (Y);
- The Identity Broker (Z) requests a login from the Identity Provider (Y);
- The Identity Provider (Y) authenticates the Human Service Consumer (Human X) (on the basis of Human X's credentials);
- The Identity Provider (Y) issues an identity assertion and authorization assertion for the Service Provider (Party B) to the Identity Broker (Z);
- The Identity Broker (Z) forwards the identity assertion and authorization assertion to the Service Provider (Party B);
- The Service Provider (Party B) validates the identity assertion and authorization assertion through the following steps:
- The Service Provider (Party B) authenticates the Identity Broker (Z) and validates its iSHARE certification;
- The Service Provider (Party B) authenticates the Identity Provider (Y) and validates its iSHARE certification.
- The Service Provider (Party B) authenticates the Human Service Consumer (Human X) based on the validity of the identity assertion, and validates the iSHARE adherence of the Service Consumer (Party A);
- The Service Provider (Party B) authorizes the Human Service Consumer (Human X) of the Service Consumer (Party A) based on the authorization assertion and the entitlement information registered with the Service Provider (Party B);
- The Service Provider (Party B) executes the requested service;
- The Service Provider (Party B) provides the service result to the Human Service Consumer (Human X).
As depicted:
Note that this use case is exactly the same as primary use case 3, as found under detailed Functional descriptions. In this section, the same use case is also explained without an Identity Broker.
...